A service account is a special type of Google account. It represents a non-human user that needs to authenticate and be authorized to access data in the Google APIs.
This page describes how to set up a service account and authorize users.
Create a service account
Section titled “Create a service account”Follow these steps to create a Google service account:
- From the Google Cloud Platform dashboard, navigate to IAM & admin > Service Accounts.
- Select your project and click Create service account.
- Enter a name, ID, and description for the Service Account.
- Click Create and continue.
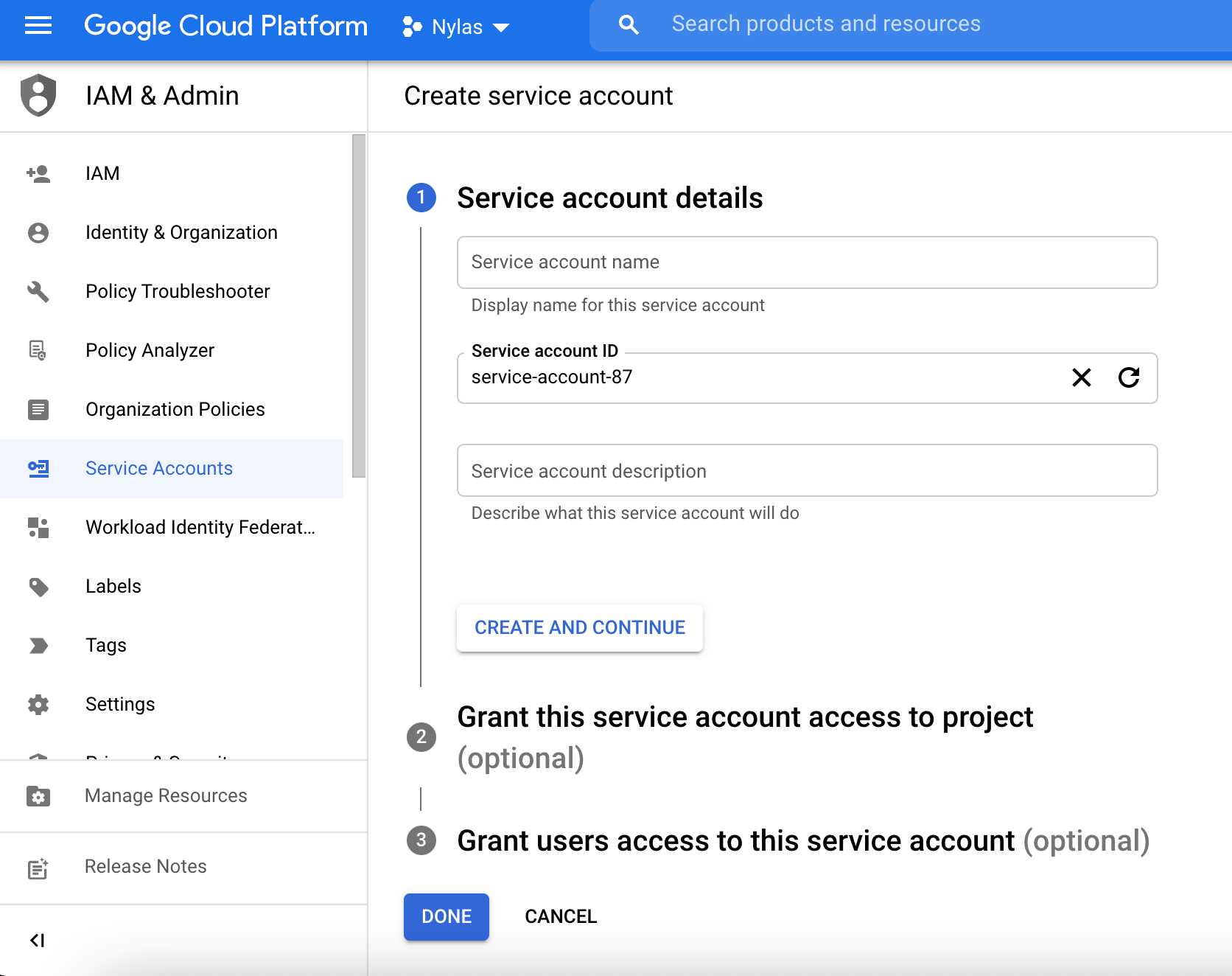
- (Optional) Grant the service account access to your GCP app.
- (Optional) Grant users access to the service account.
- Click Done.
(Optional) Create a service account key
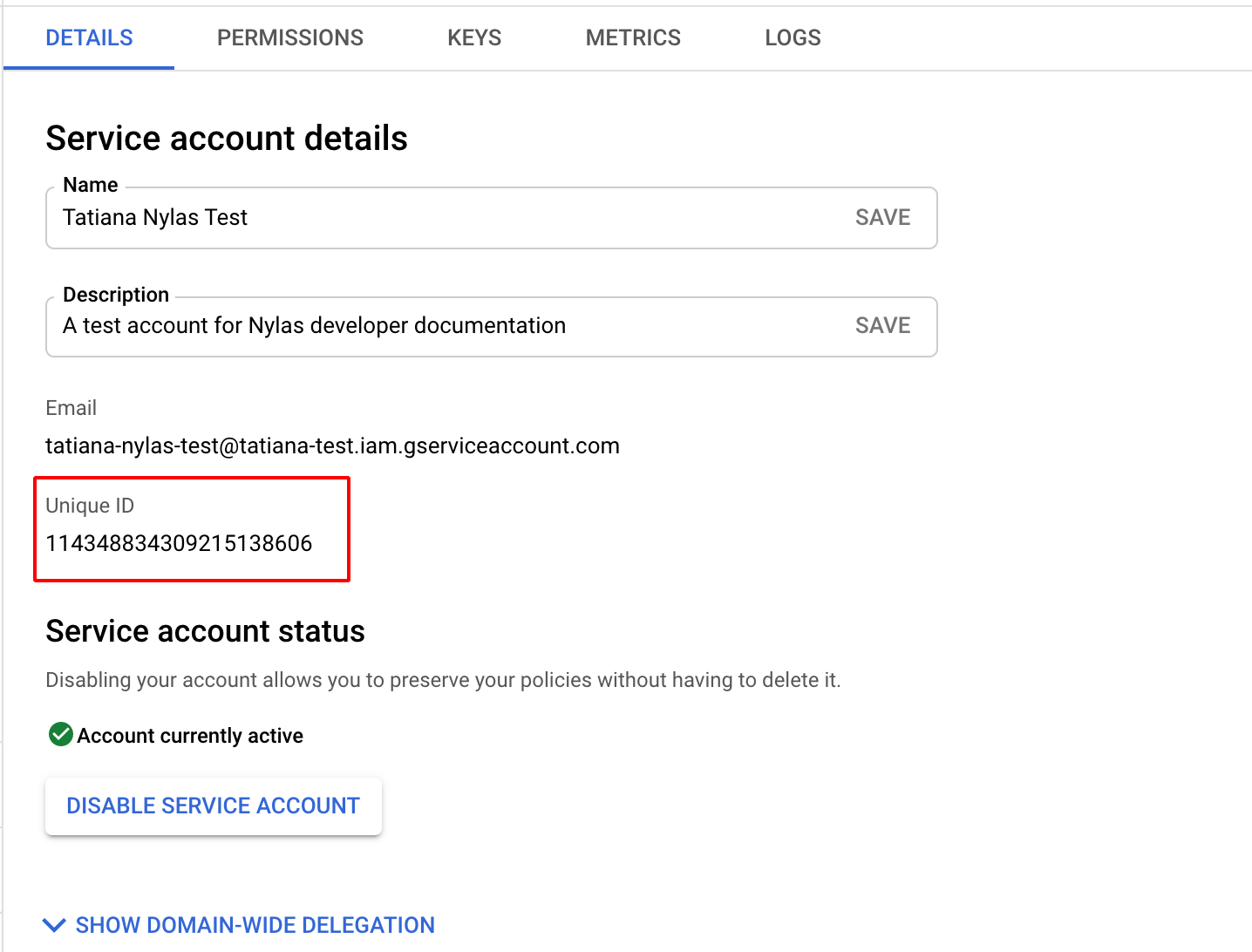
Section titled “(Optional) Create a service account key”If you choose to delegate domain-wide authority, you’ll need the client ID for your GCP app. You can access it in two ways:
- Using the service account key, if you made one.
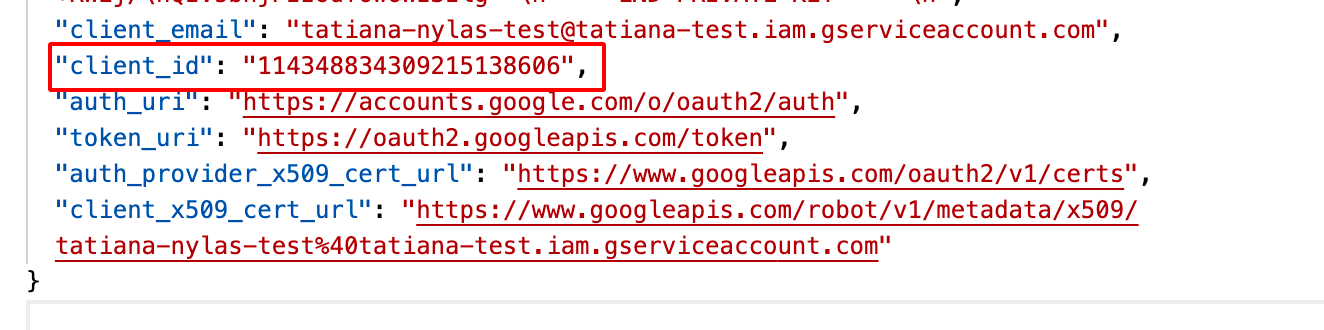
- From the Details page for your GCP app.
After you have your client ID, follow these steps to delegate domain-wide authority:
- From the Google Cloud Platform dashboard, navigate to Security > Access and data control > API controls.
- In the Domain wide delegation pane, select Manage domain wide delegation.
- Click Add new.
- Enter your GCP app’s client ID.
- Enter the following OAuth scopes:
https://www.googleapis.com/auth/userinfo.emailhttps://www.googleapis.com/auth/userinfo.profilehttps://www.googleapis.com/auth/calendarhttps://www.googleapis.com/auth/admin.directory.user.readonly
- Click Authorize.
Authenticate users with a service account
Section titled “Authenticate users with a service account”To authenticate a user with a service account’s credentials, make a Bring Your Own Authentication request. Pass the user’s email_address, and include the service account’s credential_id.
curl --request POST \ --url 'https://api.us.nylas.com/v3/connect/custom' \ --header 'Accept: application/json' \ --header 'Authorization: Bearer <NYLAS_API_KEY>' \ --header 'Content-Type: application/json' \ --data '{ "provider": "google", "settings": { "email_address": "[email protected]", "credential_id": "<GOOGLE_SERVICE_ACCOUNT_ID>" }, "scope": [ "https://www.googleapis.com/auth/userinfo.email", "https://www.googleapis.com/auth/userinfo.profile" ], "state": "my-state" }'Currently, you cannot use a service account to bulk authenticate room resources.